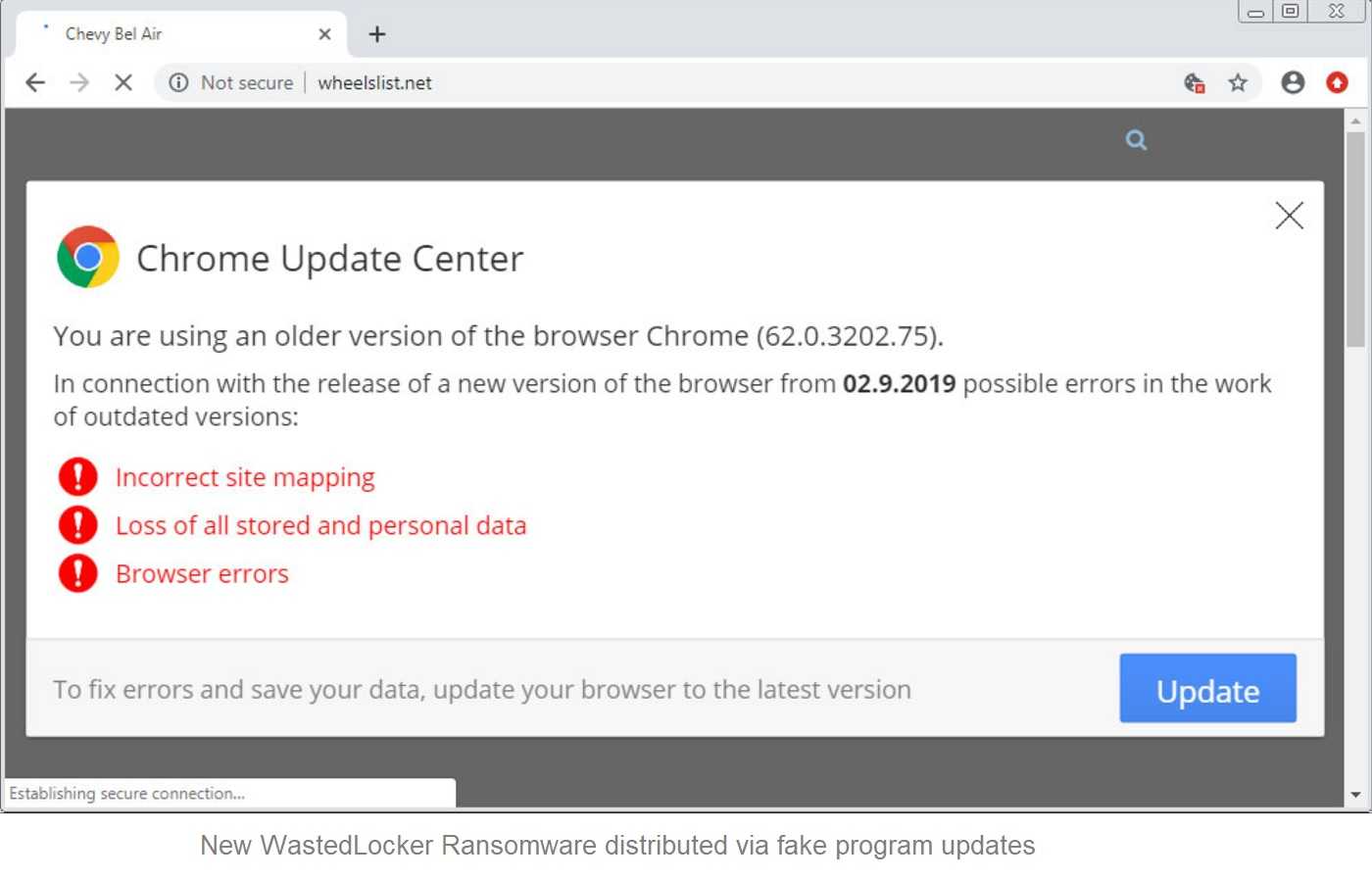
In May of this year, the world discovered an effective and stealthy ransomware known as WastedLocker. A very public attack on Garmin navigation systems alerted the cybersecurity community to the new ransomware, believed to be the work of Evil Corp, a Russian hacking group. Evil Corp is one of the most successful and prolific attack groups in the world, demanding millions in bitcoin to restore a victim’s data. The U.S. Treasury Department officially sanctioned the group last year, blaming it for some of the worst hacking and bank fraud schemes over the past decade. Perhaps it’s no surprise that Evil Corp created WastedLocker, the ransomware that enters and exits a victim’s data system entirely undetected.
The only evidence WastedLocker leaves behind is a ransom note demanding steep payments for the key to the victim’s encrypted data systems. As is typical with ransom notes, they also threaten permanent data loss will be the result of not paying up. That’s an unnerving prospect for favored ransomware targets like healthcare institutions, city services, financial institutions, law enforcement, and others that rely on constant data access to provide unhindered services for those who need them.
A deep dive into WastedLocker’s workings was done by researchers at Sophos to see what makes the ransomware tick. Overall, it’s shown the malware goes to great lengths to avoid detection, making WastedLocker the highly effective data bandit that it is. The ransomware is constructed in a way that’s meant to obfuscate conventional anti-ransomware solutions, even adding increased layers to the process to further evade security tools. The carefully planned attacks often begin with stolen login credentials. If those behind WastedLocker can steal system administrator privileges, they’ll have full control to do what they will, and that usually means it’s “game over” for the victims.
 Mitigating Ransomware Risks
Mitigating Ransomware Risks
For now, it’s up to an organization to apply cyber-safe obstacles to help thwart ransomware attacks, including those by WastedLocker. Remember, employees are often the first line of defense against cybercrime, especially email phishing. An employee who is well-trained about cyberattacks and methods can stop a threat in its tracks before it goes any further. Below are other ways to help keep WastedLocker attacks from succeeding.
- Keeping system software and security patches updated as soon as they are available helps assure the latest security measures and bug fixes are installed and ready to work.
- Strong and unique passwords should always be used and never reused, since password cracking is a hacker’s invitation to a data system.
- Using MFA (multi-factor authentication) goes a long way assuring the person logging into a work account isn’t a hacker.
- Backup system data on a regular basis. Regularly check the data restoration process to ensure it works when needed, and keep it separate from the system. If an organization can restore its own data, the need to pay a ransom is neutralized.
/HarborNetworksLogo-1.png?width=319&height=76&name=HarborNetworksLogo-1.png)