Just one of two simple, basic ingredients are needed to infiltrate an organization’s data system: weak passwords or unpatched software. A study by Positive Technologies shows 71% of companies tested had at least one of these security flaws. The study used ethical hackers (the good guys) to examine how easily an internal network can be breached if weak passwords and/or unpatched software exists within. Spoiler Alert: The answer is “very easily.” And since more people than ever are now working from home due to the pandemic, following basic security protocols are more important than ever.
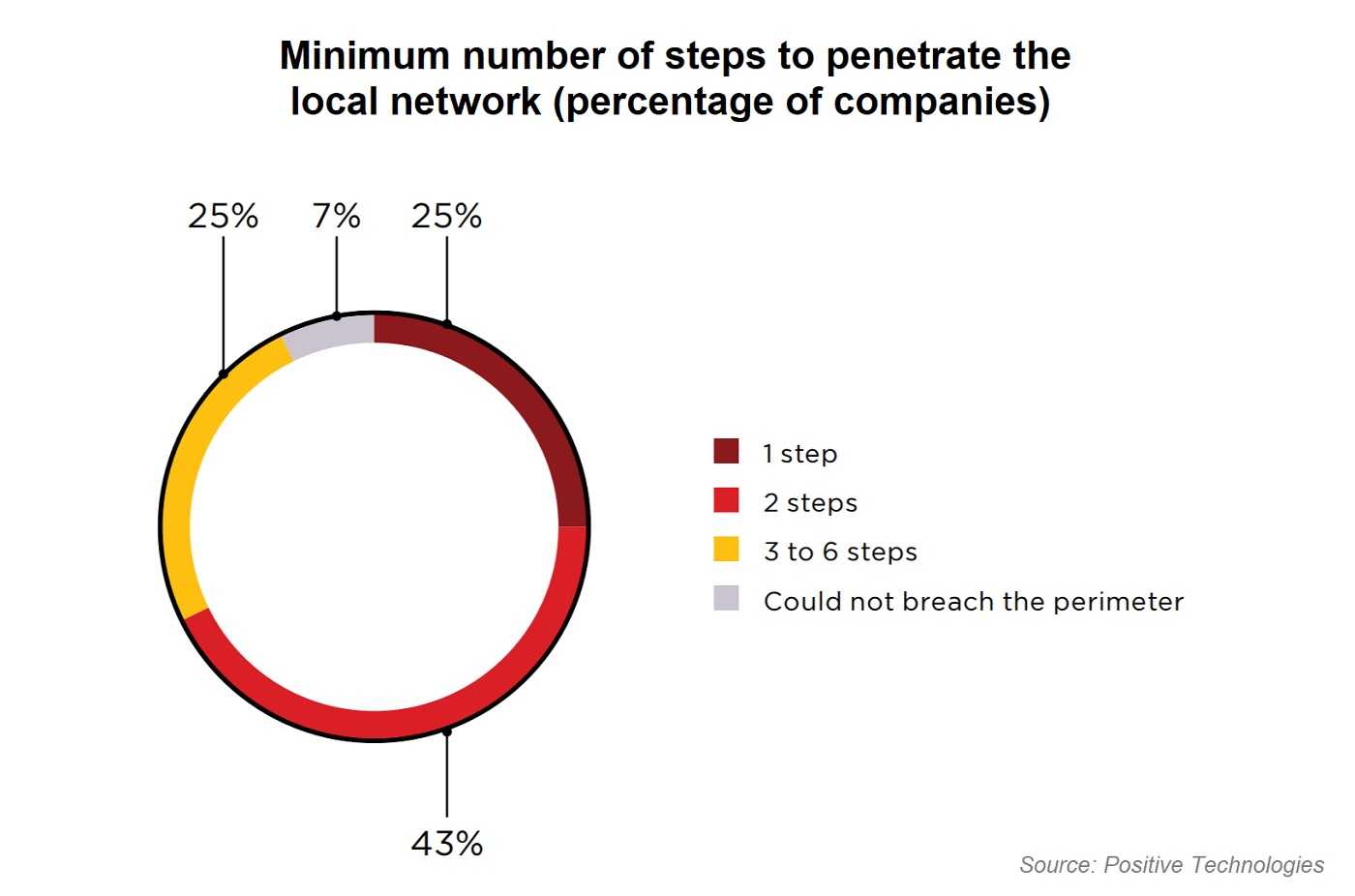
The report notes the average time for their ethical hackers to breach an internal network is four days. In one instance, an ethical hacker breached a network system in just thirty minutes. Finding almost three-quarters of companies tested had these flaws isn’t great news for corporate data security, but it is welcome news for cyberthieves. After all, regardless of any excuses for poor security protocols, the problem still remains.
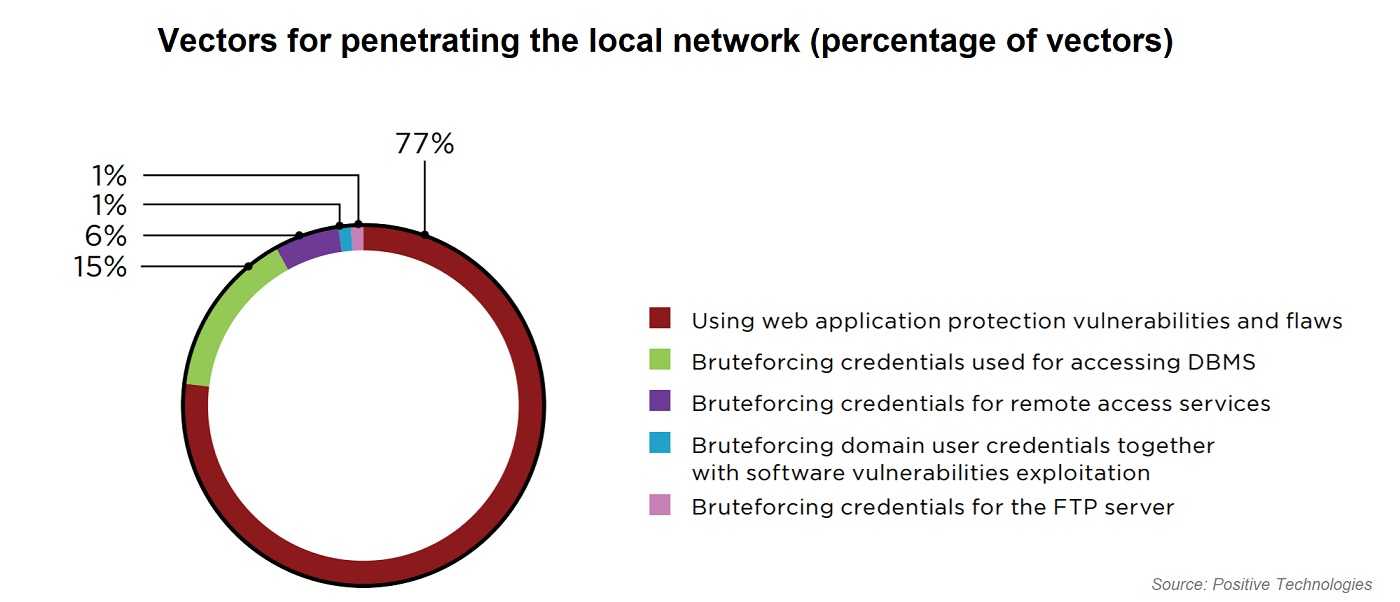
Weak passwords are one of the biggest security issues that allow openings to a network data system. Hackers use brute-force attacks that exploit poor passwords. An attacker floods a system with passwords and passphrases, often found underground for free, until a match is eventually found. Attackers can also assign the task to bots that can crack passwords much faster. Once a password is hijacked, the brute-force attack exploits system software vulnerabilities that are already known to hackers, and a system is further compromised.
Positive Technologies also finds over two-thirds of organizations in their study have software needing security updates. Any patches should always be applied as soon as possible as they often contain fixes for security bugs and other software flaws that are easily exploitable. The study also found that one-third of organizations were easily accessed using a combination of brute-force attacks along with unpatched software.
Taking basic security steps to protect a network is within the reach of most, if not all, organizations. Those continuing to ignore using fortified passwords are playing fast and loose with their data security. Doing so can put out the welcome sign for ransomware and other crippling malware cyberattacks that have devastating effects on a business. Strong passwords combined with using 2FA (two-factor) or MFA (multi-factor authentication) adds another layer of identity verification to logins, and that’s a good thing. Remember, the study finds when fortified passwords with additional verification are combined with updated software, many forms of cyberattacks can be prevented. It’s really that simple.
/HarborNetworksLogo-1.png?width=319&height=76&name=HarborNetworksLogo-1.png)