Sharing online can be irresistible, especially when quizzes, surveys and other fun opportunities allow your voice to be heard. It’s important to note that bad actors are constantly trolling social media sites for personal information. One of their biggest allies are the viral social media quizzes and surveys that pop-up on sites like Facebook. They give hackers gold nuggets of information that can be used for future cyberattacks. With online quizzes and oversharing providing the fuel for an attack, knowing it’s avoidable to begin with is perhaps most disturbing of all.
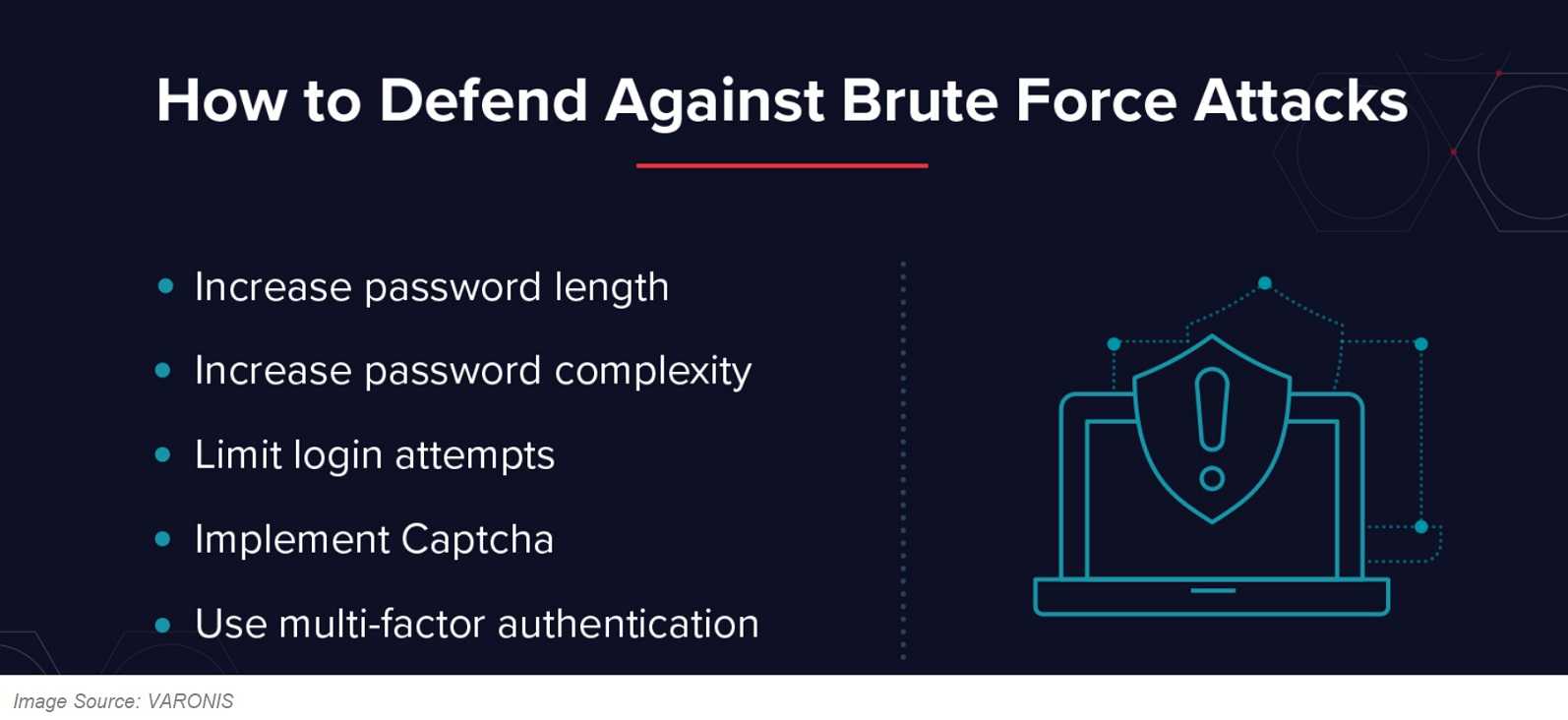
Brute force attacks on passwords succeed 50% of the time when the twenty-five most commonly used passwords are tried on a user account. Weak passwords aside, oversharing leads to hackers using that information to guess security questions and passwords. Posting the name of a pet, the high school you attended, or your best childhood friend can give hackers answers to account security questions. Also, by using automated bots, attackers can brute force a password with little effort.
Socially engineered attacks, like those using targeted email phishing, are often done using information gleaned from social media posts. Sharing that you’re an advocate for homeless animals can give a hacker a number of attention-grabbing email subject lines. The email content can include a link to a fake website and malware-filled attachments for you to open. They can also send emails that appear to be from a friend – a friend whose email account they have hijacked.
Physical crimes against private property can also be assisted by oversharing. Posting the address of your new home can, at some point, be put together with posting current vacation photos and can give a criminal the green light to enter your home knowing you’re not there. Hackers are particularly good at putting tidbits of information together, and you, your social media posts and possessions are not immune.
Tips for Smart Sharing
 Resist answering social media surveys and quizzes whenever possible, especially those asking for passwords and other personal information; be aware of coupon and promotional scams sent by those other than the official retailer; don’t follow email links or open attachments from unknown senders, and since hackers can steal email addresses from those you trust, it should be verified with the sender before acting on them.
Resist answering social media surveys and quizzes whenever possible, especially those asking for passwords and other personal information; be aware of coupon and promotional scams sent by those other than the official retailer; don’t follow email links or open attachments from unknown senders, and since hackers can steal email addresses from those you trust, it should be verified with the sender before acting on them.
- It helps to think like a hacker before posting information, meaning: Can someone use your shared information against you? Does a posted picture show your address, car license plate, credit card, or driver’s license? Remember, it’s easy to enlarge a photo until even the smallest details are visible.
- Keep anti-virus and other device software updated with the latest versions; enable 2FA (two-factor authentication) whenever possible, especially for social media sites; check that a site is properly secured with a URL that begins with “https” (the “s” at the end is a sign a site is secure) and has the lock icon on the address bar; check and double-check the URL spelling as hackers can drive you to a cleverly misspelled, exact duplicate website they control; never download apps from third party websites and get them only from the official Google Play and Apple App Store sites, or the official store for your device.
/HarborNetworksLogo-1.png?width=319&height=76&name=HarborNetworksLogo-1.png)